07/04/2026
Cyber Insights
April 2026 Cyber Brief
This month's stories share a common thread: the consequences of adopting and deploying technology without governing it are becoming specific, documented, and in some cases legally enforced.
Practical advice, industry updates, and cyber security guidance for Australian businesses — from the Jam Cyber team.
07/04/2026
Cyber Insights
This month's stories share a common thread: the consequences of adopting and deploying technology without governing it are becoming specific, documented, and in some cases legally enforced.

05/03/2026
Cyber Insights
Jam Cyber Brief March 2026 Edition March is a good moment to take stock of two things that have quietly shifted over the past few months: the compliance…

19/02/2026
Cyber Insights
OpenClaw and Australian Professional Services: The Risks You Need to Know If you haven't heard of OpenClaw yet, you will. And if you run a business in…

04/02/2026
Cyber Insights
Jam Cyber Brief February 2026 Edition This month, we’re seeing businesses feeling the weight of the “AI balancing act”. AI tools are becoming more powerful and…

04/02/2026
Blog
What Is Cyber Security in 2026 We hear it in the news constantly, but cyber security is still often misunderstood. Many businesses still associate it with…

30/01/2026
Blog
Does My Business Need Cyber Security? Are you still wondering whether cyber security is necessary for your business? In practice, the question has shifted.…

29/01/2026
Cyber Insights
How to Improve Your LastPass Security Score Cloud passwords sit at the centre of how most businesses operate. Email access, accounting systems, customer data,…

06/01/2026 • Cyber Insights
Jam Cyber Brief January 2026 Edition Welcome to our first edition of 2026, where we are beginning the year on a high! We are very proud to share that Jam Cyber…

19/12/2025 • Cyber Security Resources
Patch Operating Systems: Keep Your Business Secure and Stable Every day, cyber attackers look for businesses running outdated software. Operating system…

19/12/2025 • Cyber Security Resources
Patch Applications: Closing the Gaps Before Attackers Find Them Every business relies on software to operate smoothly. But the same tools that keep work moving…

18/12/2025 • Cyber Security Resources
Multi-Factor Authentication (MFA): Strengthening Access to Your Systems Cyber attacks often start with something as simple as a stolen or guessed password.…
08/12/2025 • Cyber Security Resources
Macro Settings: Stopping Hidden Threats in Everyday Files Cyber attacks don’t always start with an obvious threat. Sometimes, they begin with a simple Word or…

08/12/2025 • Cyber Security Resources
Regular Backups: The Safety Net Every Business Needs Cyber attacks, system failures and human errors are, unfortunately, becoming all too common for Australian…
08/12/2025 • Cyber Security Resources
Why the Essential 8 Matters for Australian Businesses Small to medium businesses (SMBs) remain the most frequent targets of cyber attacks. The Australian Cyber…

08/12/2025 • Cyber Security Resources
Application Control: The First Line of Defence in Cyber Security Cyber threats have evolved. Attackers no longer rely solely on breaking passwords or tricking…

08/12/2025 • Cyber Security Resources
Application Hardening: Strengthening the Software You Already Use Everyday business tools like browsers, PDF readers, and Microsoft Office are essential to…

04/12/2025 • Cyber Insights
Jam Cyber Brief December 2025 Edition 2025 has seen dramatic changes in the technical adoption and development for businesses globally. Additionally, the wave…
02/12/2025 • Cyber Security Resources
Remote Working Cyber Security: How to Build a Cyber Safe Remote Workforce Remote and hybrid work are now permanent features of the modern workplace. For many…

02/12/2025 • Cyber Security Resources
Restricting Administrative Privileges: Keeping Control of Who Has Control When too many people have unrestricted access to systems, small mistakes or malicious…
03/11/2025 • Cyber Insights
Jam Cyber Brief November 2025 Edition This month’s cyber brief focuses on human risk and shared responsibility. Cyber security technology is now a given, which…

07/10/2025 • Cyber Insights
Jam Cyber Brief October 2025 Edition October marks Cyber Security Awareness Month, a reminder that protecting your business doesn’t have to be complicated.…
25/09/2025 • Blog
When Your Identity Is Under Attack: A Practical Playbook for Aussies We use online services for everything from banking and shopping to health and government…
18/09/2025 • Cyber Security Resources
Rights Management in Word, Excel, and PowerPoint: Why It Matters and How to Set It Up Information is one of the most valuable assets in any business. For small…
08/09/2025 • Cyber Insights
Jam Cyber Brief September 2025 Edition From the rise of quantum computing and AI-native graduates entering the workforce, through to the risks of shadow IT and…
07/08/2025 • Cyber Insights
Jam Cyber Brief August 2025 Edition This month’s brief covers several key developments that will affect how firms operate and respond to cyber threats. We look…

14/07/2025 • Cyber Security Resources
Employee Onboarding and Offboarding: A Positive Approach to IT Security Employee onboarding and offboarding are commonly considered HR functions. But they also…
07/07/2025 • Cyber Insights
Jam Cyber Brief July 2025 Edition This month’s edition of the Jam Cyber Brief brings you a clear look at the trends, tools, and threats shaping Australia’s…
01/07/2025 • Cyber Insights
Best Practices for Creating and Managing Strong Passwords for Small Businesses Passwords are often the primary line of defence against unauthorised access, and…
12/06/2025 • Cyber Insights
Jam Cyber Brief June 2025 Edition Cyber and technology insights for Australian firms and small to medium businesses The Jam Cyber Brief delivers focused,…

07/04/2025 • Cyber Insights
Uncertainty Creates Opportunity: How Cyber Criminals Exploit Change In times of uncertainty, businesses and individuals alike seek stability. Unfortunately,…

14/03/2025 • Cyber Insights
The Cascade Effect: How Small Cyber Security Mistakes Lead to Big Business Disruptions Cyber security often feels like something businesses only think about…
21/02/2025 • Cyber Security Resources
How to Configure Email Forwarding Rules Safely in Office 365 Email forwarding rules in Office 365 can be a convenient way to streamline communication, but they…
20/02/2025 • Cyber Insights
The 10 Most Notorious Cyber Crime Gangs in 2025 Over the past 24 months, some familiar names have maintained their grip on the cyber underworld, while new and…
22/01/2025 • Cyber Insights
Top 10 Insights from the Annual Cyber Threat Report 2023–2024: A Business Perspective For the cyber enthusiast among us, the Annual Cyber Threat Report by the…

18/12/2024 • Cyber Insights
Stay safe this 'Silly Season' As the festive season approaches, it’s a time for joy, generosity, and, unfortunately, heightened cyber risks. For business…

30/10/2024 • Cyber Security Resources
The Importance of DMARC Monitoring Against Cyber Criminal Impersonation One of the most insidious cyber threats is email-based impersonation. It is a strategy…

14/10/2024 • Cyber Insights
The Pros (and Cons!) of ISO 27001 for Australian SMEs Each year, the number of cyber risks faced by small and medium-sized enterprises (SMEs) increases. These…
30/09/2024 • Cyber Security Resources
Should my business use AI? Business owners across all industries are asking the question: should we use AI? For most, the answer will not be “yes or no” but…
16/09/2024 • Cyber Insights
The Benefits of Restricting USB Access for Employees One of the most underestimated measures for protecting an organisation's data is the restriction of USB…

30/08/2024 • Cyber Security Resources
What is VoIP and how can it help cyber security? As businesses grow and adapt to new challenges, the demand for reliable, cost-effective, and scalable…
13/08/2024 • Cyber Insights
How and Why to Block HTM/HTML Attachments in Outlook 365 Microsoft Outlook 365 is one of the most popular business communication tools. However, a particular…

05/08/2024 • Cyber CEO
https://youtu.be/aXxbtvJ1vts Cyber CEO – How to secure your passwords Using Password Management The importance of securing our passwords cannot be overstated.…
22/07/2024 • Cyber Security Resources
What Does a Managed Service Provider Do? Staying ahead of technological advancements and maintaining strong cyber security measures can add extra time and…

19/07/2024 • Cyber Insights
Building a Positive Cyber Security Culture A successful cyber security culture starts at the top. We often hear the term “a great company culture”. This is…

08/07/2024 • Cyber CEO
https://youtu.be/FI5iivYvW3w Cyber CEO - Phishing Emails Welcome to our phishing guide, a scam where people are tricked into giving personal information…
24/06/2024 • Cyber Security Resources
Understanding Whitelisting: A Simple Guide for Business Owners One effective security measure that can significantly enhance your protection is "whitelisting."…
12/06/2024 • Cyber Insights
Understanding Administrative Privileges: A Guide for Small Business Owners What Are Administrative Privileges? Administrative privileges on computers, simply…
07/06/2024 • Tips & Resources
Remote Monitoring & Management (RMM) Agent In this article What is RMM? RMM Agent Installation Process 1: Download the file: AgentSetup_CLIENT_NAME.exe 2:…

07/06/2024 • Tips & Resources
Installing Programs or Apps In this article Before you start What are MAP and PolicyPaK Installing a new program or app Step 1: standard install process Step…
07/06/2024 • Tips & Resources
Duo Multi-Factor Authentication (MFA) Installation Guide In this article What is MFA and Duo? Step 1: Duo MFA Smartphone (or tablet) App Installation Step 2:…
05/06/2024 • Tips & Resources
LastPass: Set SMS Account Recovery 1. While logged in to your LastPass account, click Account Settings. Under General tab, scroll down and click ‘Update Phone’…
05/06/2024 • Tips & Resources
LastPass: Enable Multi-factor Authentication 1. While logged in to your LastPass account, click Account Settings and click on ‘Multifactor Options’. Look for…

03/06/2024 • Cyber CEO
https://youtu.be/0T3oG2I4av4 Cyber CEO - What is Log4J hack? In this video, we dive into the Log4j hack, a significant vulnerability that emerged in December…

27/05/2024 • Cyber Security Resources
Should you tell your customers if you have been hacked? There are many facets to address when dealing with a cyber attack. This include the ‘technical’ side,…
24/05/2024 • Cyber Insights
Fake Invoice Scams: How to Protect Your Business & Your Customers Fake invoice scams involve the unauthorised sending of invoices that are designed to look…
06/05/2024 • Cyber CEO
https://www.youtube.com/watch?v=3-Br0X7-uls Cyber CEO – Managed Services Provider Welcome to Cyber CEO! This video provides an overview of Managed IT Services…
23/04/2024 • Cyber Insights
Next-Generation Antivirus vs. Traditional Antivirus: what’s right for your business? As cyber threats evolve, the way we counteract these threats must also…
22/04/2024 • Cyber Security Resources
Why Business Owners Should Know About The Essential Eight With the increasing sophistication of cyber threats, Australian businesses, especially small and…
08/04/2024 • Cyber CEO
https://youtu.be/s6DWPHJqDwg Cyber CEO – DNS Based Protection or WebProtect As part of our Cyber CEO series, we're exploring essential tools and strategies to…
25/03/2024 • Cyber Security Resources
//Cybersecurity for business 16 Ways to Spot a Phishing Email: Your Guide to Safer Inboxes With our businesses becoming more digital, the need for heightened…
11/03/2024 • Cyber Insights
Blocking HTM/HTML Attachments In Google Workspace Understanding how to enhance email security within Google Workspace is important for protecting sensitive…

04/03/2024 • Cyber CEO
https://youtu.be/azRfbm7_dw8 Cyber CEO – Man-in-the-Middle Attacks Welcome to another Cyber CEO video. Here, we focus on man-in-the-middle attacks, which pose…
26/02/2024 • Cyber Security Resources
What is a notifiable data breach? In today's digitally connected world, cyber security is more critical than ever. One vital aspect of cyber security that has…
16/02/2024 • Cyber Insights
Understanding Microsoft 365 Licences: An Overview for SMEs Navigating the complexities of software licensing can be an exhausting task for small and…
05/02/2024 • Cyber CEO
https://youtu.be/AqZ55mH6Pro Cyber CEO – Administrative Privileges Welcome to our Cyber CEO series, where we break down complex IT and cyber security concepts…

22/01/2024 • Cyber Security Resources
The new frontier of email fraud If you received an urgent, realistic request from your manager via email, that sounded like them and used internal/industry…
15/01/2024 • Cyber CEO
https://www.youtube.com/watch?v=hJSLemvR-pg Cyber CEO – ACSC Essential 8 Welcome to another Cyber CEO video series, where we break down key cyber security…

15/01/2024 • Cyber Insights
Understanding Multi-Factor Authentication: What it is and why you probably need it Multi-Factor Authentication (MFA) is a security feature now commonly seen in…
18/12/2023 • Cyber Security Resources
What is an Incident Response Plan? The primary purpose of an Incident Response Plan is to provide all employees, including the Management Team, with a clear…
04/12/2023 • Cyber CEO
https://youtu.be/yT8gwnXHkEQ Cyber CEO – Ransomware Cyber security has become a major concern for businesses of all sizes. To help business leaders and owners…
02/12/2023 • Cyber Insights
The Menace of Malware: Safeguarding Small Businesses In the expansive landscape of cybersecurity threats, few adversaries loom as ominously as malware, posing…

16/11/2023 • Cyber Insights
Minimising the Risk of Insider Threats for Your Business In the constantly evolving landscape of cybersecurity, one aspect that is frequently underestimated is…

06/11/2023 • Cyber CEO
https://youtu.be/hvwIZJuL5xY Cyber CEO – Application Whitelisting Welcome to another video of the Cyber CEO series, where we break down complex cyber security…

16/10/2023 • Cyber Insights
Cyber Security Strategies: Enabling Small Businesses to Collaborate with Major Sectors Australian small to medium businesses (SMBs) are progressively realising…

02/10/2023 • Cyber CEO
https://youtu.be/U1yOzb-ZIhE Cyber CEO – Multifactor Authentication Welcome to Cyber CEO! In this blog, we’re diving into multifactor authentication (MFA),…
29/09/2023 • Cyber Insights
Navigating the Risks: The Dangers of Using Public Wi-Fi Networks In our interconnected world, staying connected is a necessity for businesses and individuals…

04/09/2023 • Cyber CEO
https://youtu.be/gVmTQRbqtdA Cyber CEO – Cyber Security For Business Welcome to Cyber CEO, where we explain cyber security terms and concepts for businesses.…

07/08/2023 • Cyber CEO
Cyber CEO – Application Hardening Short videos explaining things around cyber threats and cyber security for small and medium business. This session asks “…

12/06/2023 • Cyber Insights
Do you know your legal and ethical obligations if your business experiences a cyber attack? A cyber attack can be devastating for a business. In fact, 22% of…
08/05/2023 • Cyber Insights
10 ways to ensure your business is protected from the Log4j vulnerability In December 2021, a vulnerability was discovered in a Java code known as the Log4j…
10/04/2023 • Cyber Insights
Australian Cyber Security Centre warning Australia may end up in cyber warfare “crossfire” according to a warning from the Australian Cyber Security Centre…

13/03/2023 • Cyber Insights
Australian Cyber Security Policies and Procedures Cyber security is not just about software, tools, and systems. Having clear policies and procedures in place…

13/02/2023 • Cyber Insights
What’s Your CYBER RISK? Do you know what your cyber risk is? Unfortunately, some industries and business structures are at more risk of a cyber attack than…

16/01/2023 • Cyber Insights
Shields Up Warning by the U.S. Government’s Cyber Security & Infrastructure Agency (CSIA) Yesterday, the U.S. Government’s Cyber Security & Infrastructure…

19/12/2022 • Cyber Insights
Log4J, The Cyber Security Threat of the Decade? LOG4J, the cyber security threat of the decade? As you may have seen in the media, there has been a major cyber…

05/12/2022 • Cyber Insights
Cyber Security Awareness – Think Before You Click. Employees are crucial in implementing a #CyberSecurity strategy. Unfortunately, even the most loyal and…
14/11/2022 • Cyber Insights
The Ultimate Enterprise Ransomware Guide A recently released in-depth ransomware guide by Sonicwall is the cure for insomnia for most, but really well written…

10/10/2022 • Cyber Insights
Ransomware hackers find vulnerable target in U.S. grain supply Another day, another (Agri) ransomware cyber attack. This time the US grain supply chain.…

12/09/2022 • Cyber Insights
Impact of Cyber Attacks on Law Firms in Australia Cyber attacks against businesses are on the increase globally; a trend that has accelerated due to the COVID…

08/08/2022 • Cyber Insights
Biggest Cryptocurrencies hack in history (to date) Is Blockchain really un-hackable? Crypto operators are NOT: US$600m went AWOL yesterday when Poly Network…
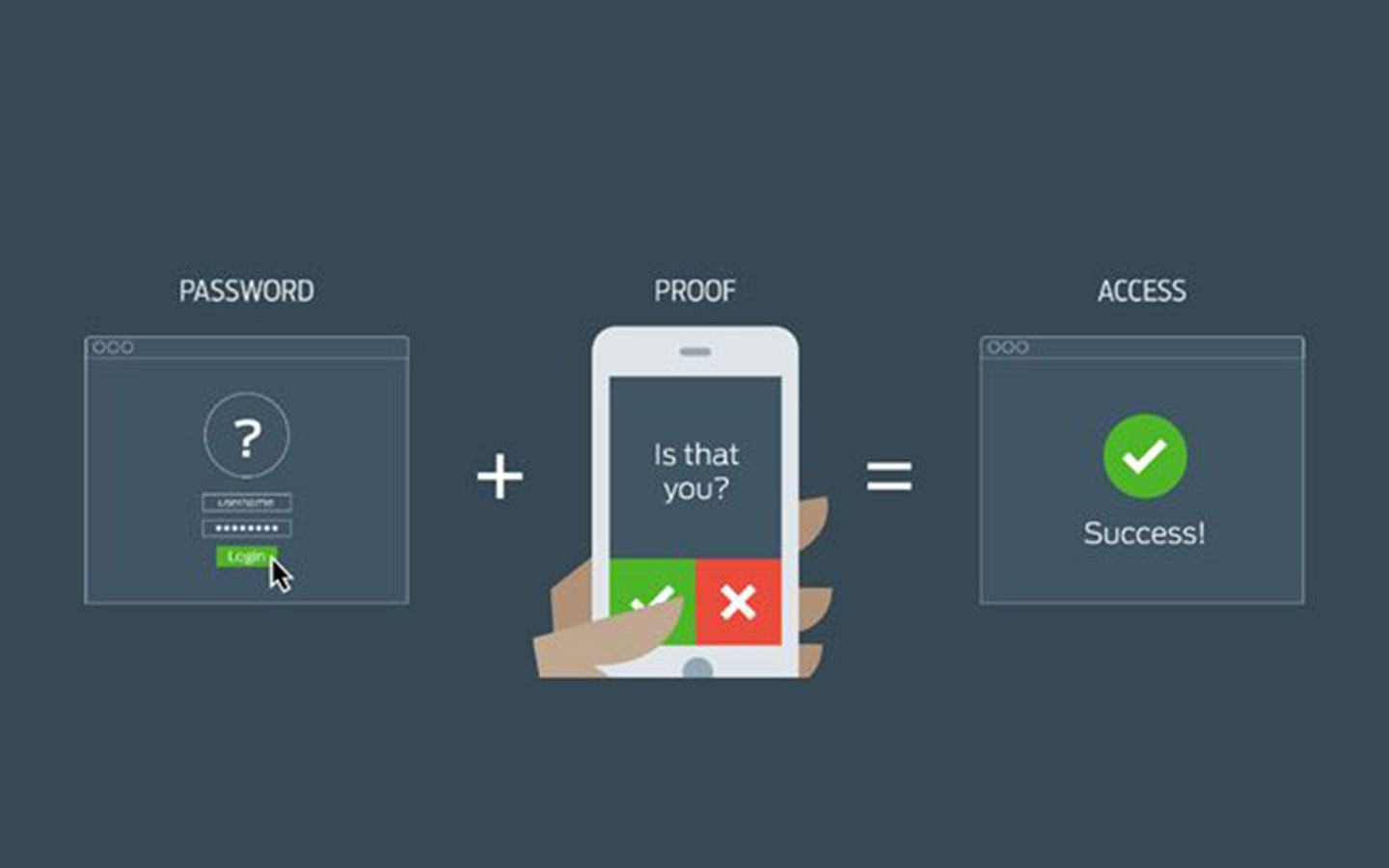
11/07/2022 • Cyber Insights
Multifactor Authentication (MFA / 2FA) for email account protection. Your email account is the crown jewels equivalent of ID theft and cyber attacks. Which is…
13/06/2022 • Cyber Insights
1m computers affected, $US70m ransomware demand – Ransomware as a Service made scalable by means of a supply chain attack! Similar to the Solarwinds hack last…

09/05/2022 • Cyber Insights
Cybersecurity and the other 99.8% It is not hard to see why the majority of small to medium enterprise (SME) owners in Australia feel that a cyber-attack would…

14/03/2022 • Cyber Insights
How many is too many passwords? That is 191 passwords for 191 accounts. So, we can all be forgiven for using the same username and password for multiple…
14/02/2022 • Cyber Insights
Advisory 2020-008 The Australian Government’s Cyber Security Centre (ACSC) has titled the attacks ‘Copy-paste compromises’ and has announced on its website…